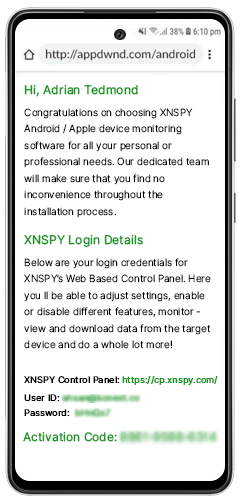

What is Xnspy Remote Keylogger and How Does It Work on Android?
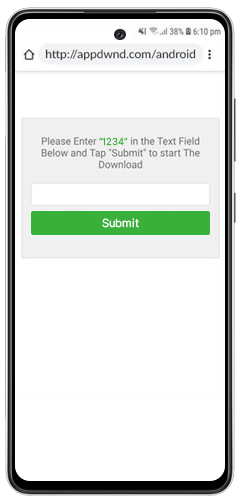
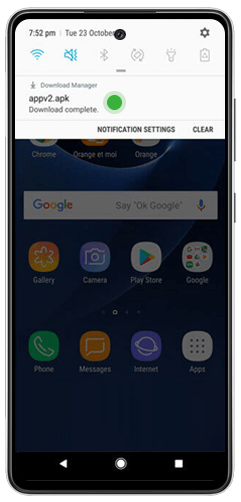
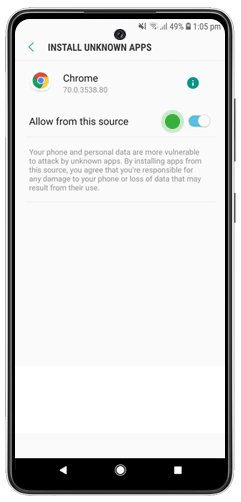
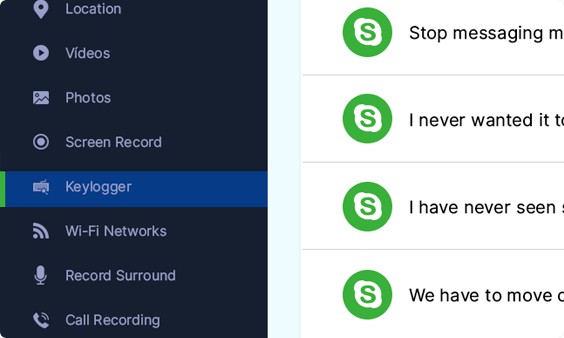
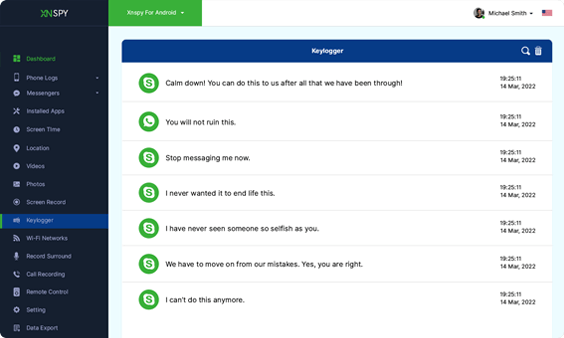
Xnspy keylogger software works surreptitiously in the background of mobile and computer devices. It keeps track of every key the device's owner types. The system then receives commands with each keystroke.
These commands may include information about the keystroke's size, time, name, and duration. Symbols, numbers, and alphabets are all permitted as keystrokes, and case matters. If you're looking for a remote keylogger for Android and want to know more on how Xnspy keylogger works, read on!